News / packet hacking village
Schedule of Packet Hacking Village Talks at DEF CON 31
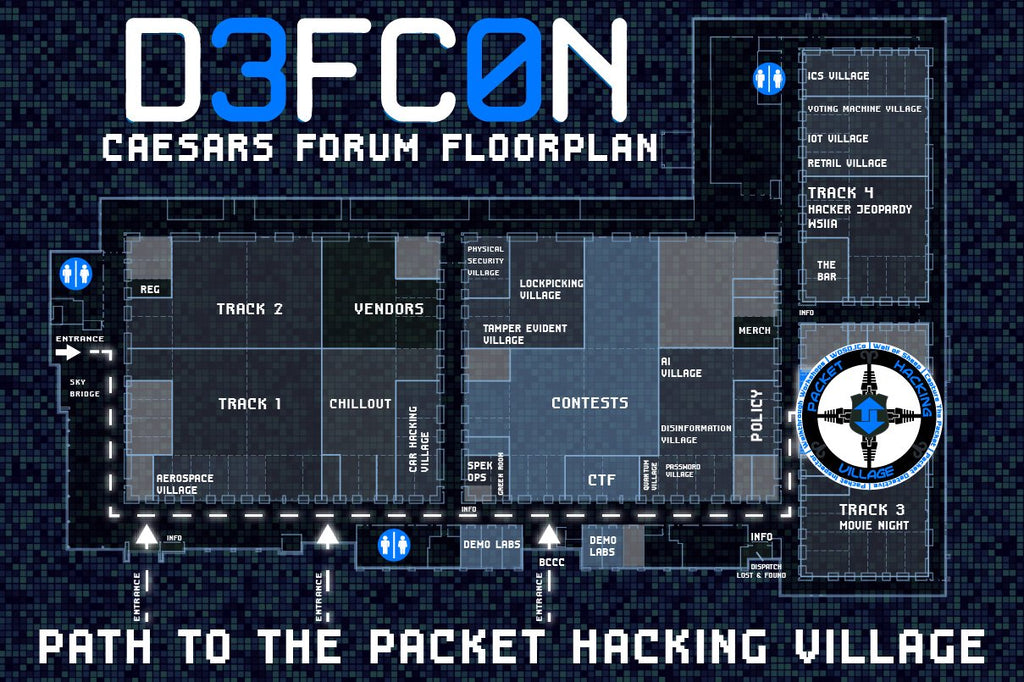
All talks will be held at the Village Stage in the Contest Area. You can enter via Room 232.
Friday
- 10:00: Pwning the Pwners with Mindware by Frank "D9" DiGiovanni
- 11:00: Death by 1000 Likes: How Much Do You Really Leak in Social Media? by Will Kay
- 12:00: OSINT for Physical Security Intelligence by Mike Raggo and Chet Hosmer
Saturday
- 15:00: WINE Pairing with Malware by Jared Stroud
- 16:00: The Importance of Arts and Crafts in ThreatOps by Pete Hay
Title: Pwning the Pwners with Mindware
Speaker: Frank "D9" DiGiovanni
Abstract: Traditionally the cyber attacker has an asymmetric advantage over the cyber defender. But does it have to be that way? Is it possible for the cyber defender to take an "offensive stance." This talk will show how the emerging science of cyberpsychology and the leveraging of AI can provide the defender with the ability to pwn the most vulnerable component in the cyberattack kill chain, the attack's human operator. Leveraging the DoD's "Tularosa Study," this talk will cover a theoretical framework for achieving this objective, outline an operational vignette, and then cover some the specifics for such an approach.
Speaker Bio: Forty-one years of government service, Frank DiGiovanni is a retired USAF Colonel and DoD Senior Executive Service. Co-Led with the DoD CIO the development of the SecDef's DoD Cyber Workforce Strategy. Built from scratch a six-month DoD Cyber Operations training course, repurposed DEFCON's CTF and CTP technical architecture to support DoD cyber operations training, and now working advanced cyber R&D projects in private sector. UPENN doctoral dissertation examined what makes hackers extraordinary unique from the average human population.
Title: The Importance of Arts and Crafts in ThreatOps
Speaker: Pete Hay, Editor-in-Chief, TheCyber.Report
Abstract: Cybersecurity professionals spend an huge amount of time attempting to use a visual medium to communicate complicated concepts in a simple yet information-dense manner. However if you ask 10 analysts to map out the same incident, you'll get 10 divergent diagrams. In this presentation we present a method of leveling-up your cybersecurity-related arts and crafts skills: effectively diagramming incidents, threat reports, threat intel, and reporting to support full-spectrum ThreatOps.
Speaker Bio: In addition to being SimSpace's Principal Security Strategist, Pete is the Co-Founder & Editor-in-Chief of TheCyber.Report. Pete has an extensive & diverse background in technology driven fields including Computer Network Operations (CNO), Network Forensics, & Nuclear Chemistry, as well as one of the few patents issued in Cybersecurity & ZTA. A life-long learner & security enthusiast, Pete helps Fortune 10 banks test & refine their security postures, while running TheCyber.Report as a passion project.
Title: Death by 1000 Likes: How Much Do You Really Leak in Social
Media?
Speaker: Will Kay
Abstract: As lonely Aussies attending our first Defcon last year, we were frequently drawn to the hilarity/uniquness of the Wall of Sheep board. One of our group suggested people leaking at the con was super entertaining, but what about throughout the rest of the year? We decided to use the time between DC30 and DC31 scraping the r/defcon subreddit to create the Wall of Sheep - online edition.
Speaker Bio: Will works for a private security consultancy in Australia. He is cybersecurity advisor and insider threat consultant. His professional career began many years ago in military intelligence to which he owes his knowledge of traditional targeting methods. The organisation and team he works for today provides security awareness and reinforcement training. His passion is removing the weakness that exists across society to social engineering techniques, and believes a more secure and prosperous future begins with people.
Title: OSINT for Physical Security Intelligence
Speakers: Mike Raggo, Security Researcher, SilentSignals; Chet Hosmer,
Chief Scientist
Abstract: Organizations seek rapid intelligence about critical situations that impact their teams, locations, or assets. Yet when it comes to OSINT we find organizations performing Open Source Information gathering; wasting time sifting through data to get to the actionable intelligence. In this presentation we demonstrate how to collect curated data and eliminate 99% of the time spent on reliminary data analysis. Furthermore, all of this data can be combined to perform trending and predictive analysis for natural disasters, geo-political situations, or business risk. The goal is to provide attendees with ideas for formulating new approaches for physical security OSINT.
Speaker Bios: Michael T. Raggo has over 30 years of security research experience. During this time, he has uncovered and ethically disclosed vulnerabilities in products including Samsung, Checkpoint, and Netgear. Michael is the author of "Mobile Data Loss: Threats &Countermeasures" and "Data Hiding" for Syngress Book. He is also a frequent presenter at security conferences, including Black Hat, DEF CON, Gartner, RSA, DoD Cyber Crime, OWASP, SANS. He was also awarded the Pentagon's Certificate of Appreciation.
Chet Hosmer is an international author, educator, researcher, and founder of Python Forensics, Inc., a non-profit research institute focused on the collaborative development of open source investigative technologies using the Python programming language. Chet is also a Visiting Professor at Utica College in the Cybersecurity Graduate Program, where his research and teaching is focused on data hiding, active cyber defense and security of industrial control systems. Additionally, Chet is an Adjunct Professor at Champlain College in the Digital Forensics Graduate Program, where his research and teaching is focused on solving hard digital investigation problems using the Python programming language.
Title: WINE Pairing with Malware
Speaker: Jared Stroud, Lead Security Engineer, The MITRE Corporation
Abstract: The growing popularity of playing AAA Windows video games on Linux has increased the compatibility of tools such as WINE and Proton. These same platforms that enable the latest games to run also can be used to execute the latest Malware. This talk will walk through configuring an environment to rapidly collect IoCs from unknown samples without having to use expensive sandboxes. Learn how to leverage your favorite UNIX tools to awk, grep, and pipe your way to extracting valuable forensic evidence without submitting your samples to $VENDOR. More on the offensive side? Come see how to shorten the feedback loop from idea generation, to testing and finally deployment!
Speaker Bio: Jared Stroud is a Lead Security Engineer at The MITRE Corporation tackling problems related to Container and Kubernetes security. Jared also contributes to ATT&CK via Adversary Emulation for Linux threats.
Packet Hacking Village Talks at DEF CON 31
Talks at DEF CON 31. Times and location of talks will be announced
soon.
**********
Title: Pwning the Pwners with Mindware
Speaker: Frank "D9" DiGiovanni
Abstract: Traditionally the cyber attacker has an asymmetric advantage
over the cyber defender. But does it have to be that way? Is it
possible for the cyber defender to take an "offensive stance." This
talk will show how the emerging science of cyberpsychology and the
leveraging of AI can provide the defender with the ability to pwn the
most vulnerable component in the cyberattack kill chain, the attack's
human operator. Leveraging the DoD's "Tularosa Study," this talk will
cover a theoretical framework for achieving this objective, outline an
operational vignette, and then cover some the specifics for such an
approach.
Speaker Bio: Forty-one years of government service, Frank DiGiovanni
is a retired USAF Colonel and DoD Senior Executive Service. Co-Led
with the DoD CIO the development of the SecDef's DoD Cyber Workforce
Strategy. Built from scratch a six-month DoD Cyber Operations training
course, repurposed DEFCON's CTF and CTP technical architecture to
support DoD cyber operations training, and now working advanced cyber
R&D projects in private sector. UPENN doctoral dissertation examined
what makes hackers extraordinary unique from the average human
population.
**********
Title: The Importance of Arts and Crafts in ThreatOps
Speaker: Pete Hay, Editor-in-Chief, TheCyber.Report
Abstract: Cybersecurity professionals spend an huge amount of time
attempting to use a visual medium to communicate complicated concepts
in a simple yet information-dense manner. However if you ask 10
analysts to map out the same incident, you'll get 10 divergent
diagrams. In this presentation we present a method of leveling-up your
cybersecurity-related arts and crafts skills: effectively diagramming
incidents, threat reports, threat intel, and reporting to support
full-spectrum ThreatOps.
Speaker Bio: In addition to being SimSpace's Principal Security
Strategist, Pete is the Co-Founder & Editor-in-Chief of
TheCyber.Report. Pete has an extensive & diverse background in
technology driven fields including Computer Network Operations (CNO),
Network Forensics, & Nuclear Chemistry, as well as one of the few
patents issued in Cybersecurity & ZTA. A life-long learner & security
enthusiast, Pete helps Fortune 10 banks test & refine their security
postures, while running TheCyber.Report as a passion project.
**********
Title: Death by 1000 Likes: How Much Do You Really Leak in Social
Media?
Speaker: Will Kay
Abstract: As lonely Aussies attending our first Defcon last year, we
were frequently drawn to the hilarity/uniquness of the Wall of Sheep
board. One of our group suggested people leaking at the con was super
entertaining, but what about throughout the rest of the year? We
decided to use the time between DC30 and DC31 scraping the r/defcon
subreddit to create the Wall of Sheep - online edition.
Speaker Bio: Will works for a private security consultancy in
Australia. He is cybersecurity advisor and insider threat
consultant. His professional career began many years ago in military
intelligence to which he owes his knowledge of traditional targeting
methods. The organisation and team he works for today provides
security awareness and reinforcement training. His passion is removing
the weakness that exists across society to social engineering
techniques, and believes a more secure and prosperous future begins
with people.
**********
Title: OSINT for Physical Security Intelligence
Speakers: Mike Raggo, Security Researcher, SilentSignals; Chet Hosmer,
Chief Scientist
Abstract: Organizations seek rapid intelligence about critical
situations that impact their teams, locations, or assets. Yet when it
comes to OSINT we find organizations performing Open Source
Information gathering; wasting time sifting through data to get to the
actionable intelligence. In this presentation we demonstrate how to
collect curated data and eliminate 99% of the time spent on
preliminary data analysis. Furthermore, all of this data can be
combined to perform trending and predictive analysis for natural
disasters, geo-political situations, or business risk. The goal is to
provide attendees with ideas for formulating new approaches for
physical security OSINT.
Speaker Bios: Michael T. Raggo has over 30 years of security research
experience. During this time, he has uncovered and ethically disclosed
vulnerabilities in products including Samsung, Checkpoint, and
Netgear. Michael is the author of "Mobile Data Loss: Threats &
Countermeasures" and "Data Hiding" for Syngress Book. He is also a
frequent presenter at security conferences, including Black Hat, DEF
CON, Gartner, RSA, DoD Cyber Crime, OWASP, SANS. He was also awarded
the Pentagon's Certificate of Appreciation.
Chet Hosmer is an international author, educator, researcher, and
founder of Python Forensics, Inc., a non-profit research institute
focused on the collaborative development of open source investigative
technologies using the Python programming language. Chet is also a
Visiting Professor at Utica College in the Cybersecurity Graduate
Program, where his research and teaching is focused on data hiding,
active cyber defense and security of industrial control
systems. Additionally, Chet is an Adjunct Professor at Champlain
College in the Digital Forensics Graduate Program, where his research
and teaching is focused on solving hard digital investigation problems
using the Python programming language.
**********
Title: WINE Pairing with Malware
Speaker: Jared Stroud, Lead Security Engineer, The MITRE Corporation
Abstract: The growing popularity of playing AAA Windows video games on
Linux has increased the compatibility of tools such as WINE and
Proton. These same platforms that enable the latest games to run also
can be used to execute the latest Malware. This talk will walk
through configuring an environment to rapidly collect IoCs from
unknown samples without having to use expensive sandboxes. Learn how
to leverage your favorite UNIX tools to awk, grep, and pipe your way
to extracting valuable forensic evidence without submitting your
samples to $VENDOR. More on the offensive side? Come see how to
shorten the feedback loop from idea generation, to testing and finally
deployment!
Speaker Bio: Jared Stroud is a Lead Security Engineer at The MITRE
Corporation tackling problems related to Container and Kubernetes
security. Jared also contributes to ATT&CK via Adversary Emulation
for Linux threats.
Packet Hacking Village at DEF CON 30
The Packet Hacking Village at DEF CON 30 will be in-person only. Our village hours:
- Friday, August 12th: 10:00 - 18:00
- Saturday, August 13th: 10:00 - 18:00
- Sunday, August 14th: 10:00 - 13:00
All times are in PDT. Schedules are subject to change.

Events and Contests
- Packet Inspector
- Packet Detective
- Capture The Packet
-
Walkthrough Workshops (WTW)
- Hardwired (NEW for 2022)
- Honeypots
- Linux Trainer (NEW for 2022)
- NetworkOS: Be The Cloud (NEW for 2022)
- Regular Expressions (RegEx) Trainer (NEW for 2022)
- WoSDJCO
Packet Inspector
The perfect introduction to network analysis, sniffing, and forensics. Do you want to understand the techniques people use to tap into a network, steal passwords and listen to conversations? Packet Inspector is the place to develop these skills! For well over a decade, the Wall of Sheep has shown people how important it is to use end-to-end encryption to keep sensitive information like passwords private. Using a license of the world famous Capture The Packet engine from Aries Security, we have created a unique way to teach hands-on skills in a controlled real-time environment.
Packet Detective
Looking to upgrade your skills or see how you would fare in Capture The Packet? Come check out what Packet Detective has to offer! A step up in difficulty from Packet Inspector, Packet Detective will put your network hunting abilities to the test with real-world scenarios at the intermediate level. Take the next step in your journey towards network mastery in a friendly environment still focused on learning and take another step closer to preparing yourself for the competitive environment of Capture The Packet.
Capture The Packet
Come compete in the world's most challenging cyber defense competition based on the Aries Security Cyber Range. Tear through the challenges, traverse a hostile enterprise class network, and diligently analyze what is found in order to make it out unscathed. Not only glory, but prizes await those that emerge victorious from this upgraded labyrinth, so only the best prepared and battle hardened will escape the crucible.


Walkthrough Workshops (WTW)
Hardwired
Don't know how to make a network cable and want to learn? Has it been years? Or do you think you're a pro? Come see if you can... make the best cable at con by cut/wire/crimp.
Honeypots
You are the world's greatest hacker. You find vulnerable machine open to SSH and brute force the root credentials easily! Hooray! But wait, are you actually on a vulnerable machine full of secrets, or a honeypot logging your every keystroke?
In this half hour workshop, you'll get your very own Cowrie honeypot (https://github.com/cowrie/cowrie) running on Ubuntu, and learn how to modify it, administer it, and watch the logs for hackers in action!
This workshop is great for both advanced Linux users who want to learn a new skill or those who have never used Linux before! We'll give you command-by-command instructions along with helpful guidance and starting points if you want to go off and do something cool.
Linux Trainer
Knowing how to use the Linux command line is a critical skill for any good security practitioner. This trainer will have 10+ problems covering some of the most fundamental Linux commands. This trainer is for people new to field and for those who want to hone their Linux command line-fu.
NetworkOS: Be The Cloud
The NetworkOS workshop will take you into the mysterious world which underpins modern computing and allows people to talk across the globe. This of course being the network itself. In this workshop you will familiarize yourself with the command line of network devices. Step by step, you will configure devices to talk to each other, share information about the computers connected to them, and relay their network information and traffic between each other. No experience needed, know how to type and copy/paste.
Regular Expressions (RegEx) Trainer
Regular Expressions or RegEX are used everywhere! If you aspire to be a Pentester, Threat Hunter, Programmer, Network Engineer, DevOps or really anything in technology today, RegEx is a skill all the greats have and the majority of the industry are terrible at. Come learn or brush up on your RegEx skills in on our live trainer.
WoSDJCO
| Thursday, August 11th | Friday, August 12th | Saturday, August 13th | Sunday, August 14th | |
|---|---|---|---|---|
| 10:00 |
PHV will be doing load/unload and setup all day. Feel free to come around and say hello. If we have gear, there will be beats. |
Funktribe | Canyon | kampf |
| 11:00 | phreakocious | Y&T | kampf | |
| 12:00 | tense x phreak | Deep Therapy | Athlex | |
| 13:00 | Tense Future | Miss Jackalope | Closing Ceremony | |
| 14:00 | Y&T | icetre normal | ||
| 15:00 | Hanz Dwight | phreakocious | ||
| 16:00 | DotOrNot | tavoo | ||
| 17:00 | heckseven + pals | T A N |
DJ Bios
phreakocious (@phreakocious, https://mixcloud.com/phreakocious)
I press enter!
tense future (@tensefutur3, https://www.mixcloud.com/tensefuture/)
sync & destroy
Yesterday & Tomorrow (Y&T) (https://takeyouto.space)
I'd like to buy a vowel.
Athlex (@brokenjetpack, https://www.mixcloud.com/athlex/)
oontz oontz oontz
Canyon (@canyon289, file:///dev/null)
"Published a book and stuff. math is cool" is what someone thinks I would write in my bio.
Deep Therapy (@therapy_life, https://www.mixcloud.com/SoundboxMiami)
oontz oontz oontz
DotOrNot (@dotornot2, https://www.mixcloud.com/dotornot/)
Are you the police? No Ma'am, we're DJs
Funktribe
Hanz Dwight (https://linktr.ee/hanzdwight)
One time in 2018, he got a noise complaint for playing music in the middle of the Mojave desert.
heckseven, eg0n, bbartokk, Iggs Boson (https://heckseven.com, https://bbartokk.com)
synth freaks, massive beats, plywood boxes, spicy grooves
Icetre Normal (@IcetreNormal, https://www.youtube.com/channel/UCVY8zEm23QFbO-7LfWLR6xg)
"When I eat fire, you shouldn't think about how I'm doing it; I really do get burned. You should think about -why-..." -Penn Jillette
kampf (@nerd_show, https://www.mixcloud.com/NerdShow)
With over a decade of experience as a college radio DJ at KWCR on Nerd Show, kampf has waded long and deep through the muddied waters of electronic music, casting his rod time and again to obtain, then share the eclectic, the compelling, the sounds off the beaten path and those lesser know varieties or species. Resident DJ for the DEF CON Chillout Lounge and for DEF CON Radio on SomaFM.com. Spinning vinyl for WoS/Packet Hacking Village since DEF CON 20!
Miss Jackalope (@djjackalope, https://www.mixcloud.com/djjackalope/)
Miss Jackalope is DEF CON's resident community DJ. She has a weekly Twitch show and a legendary Jackalope Army merch store. She plays drum and bass and bass house and is known for ceiling destruction! Happy to be back at the PHV!
tavoo (https://tavoo.co, https://soundcloud.com/tavootech)
Devoted disciple of the darker electronic sounds. Specializing in murky shades of Techno, D&B, and everything in-between.
Terrestrial Access Network (T A N)
crunchy kicks and bleeps and bloops from outer space
Packet Hacking Village Workshop Tickets at DEF CON 29 Still Available
Regular tickets: $30
Student/military: $10
Non-interactive: $20
To purchase tickets, go to https://www.eventbrite.com/e/packet-hacking-village-virtual-workshops-at-dc-29-ticket-sales-registration-164777220101
Packet Hacking Village Workshops at DEF CON 29 Announced
Schedules of workshops, talks, and events at the Packet Hacking Village are available at https://www.wallofsheep.com/pages/dc29.
Workshops Schedule
| Friday, August 6, 2021 (all times PDT [GMT-7]) | |
|---|---|
| 09:00 - 11:00 |
Web App Penetration Testing Workshop Dr. Sunny Wear |
| 12:00 - 14:00 |
Hunting Evil with Wireshark Michael Wylie |
| Saturday, August 7, 2021 | |
| 09:00 - 11:00 |
APT Hunting with Splunk John Stoner |
| 12:00 - 14:00 |
Security Investigations with Splunk Robert Wagner |
| Sunday, August 8, 2021 | |
| 09:00 - 11:00 |
Intrusion Analysis and Threat Hunting with Suricata Josh Stroschein, Peter Manev |
| 12:00 - 14:00 |
Hands-On TCP Deep Dive with Wireshark Chris Greer |
Workshops Abstracts and Bios
Web App Penetration Testing Workshop
Dr. Sunny Wear, Web Security Architect and Penetration Tester
Gain hands-on experience learning how to perform web application penetration testing in this two-hour workshop with the author of the Burp Suite Cookbook, Dr. Sunny Wear. Students will learn Injections attacks such as Cross-site Scripting and SQL Injection attacks, brute-forcing tactics, and optimization techniques for Burp Suite including configurations and macros.
Dr. Sunny Wear (Twitter: @SunnyWear) is a Web Security Architect and Penetration Tester. She provides secure coding classes, creates software, and performs penetration testing against web/API and mobile applications. Sunny has more than 25 years of hands-on software programming, architecture and security experience and holds a Doctor of Science in Cybersecurity. She is a published author, "Burp Suite Cookbook", a developer of mobile apps, such as the “Burp Tool Buddy,” and is a Pluralsight content creator, "Burp Suite for Beginners/Advanced/Writing Plugins". She regularly speaks and holds classes at security conferences such as Defcon, Hackfest, and BSides.
Hunting Evil with Wireshark
Michael Wylie, MBA, CISSP, Sr. Manager, Threat Hunting
This workshop will take attendees’ Wireshark skills to the next level with a heavy emphasis on incident response, threat hunting, and identifying anomalous network traffic. This workshop will begin with a brief introduction to Wireshark and other Network Security Monitoring (NSM) tools/concepts. Throughout the workshop, we’ll examine what different attacks and malware look like while using Wireshark. Attendees will then have hands-on time in the lab to search for Indicators of Compromise (IOCs) and TTPs utilizing staged packet capture files. Labs start out easy and quickly progress in difficulty. There will be plenty of take-home labs for additional practice.
Michael Wylie, MBA, CISSP (Twitter: @TheMikeWylie) is the Sr. Manager of a threat hunting team. In his role, Michael is responsible for managing a global team of analysts hunting for hands-on keyboards activity within customer environments. Michael has developed and taught numerous courses for the U.S. Department of Defense, DEFCON, Universities, and for clients around the world. Michael is the winner of numerous SANS challenge coins and holds the following credentials: CISSP, CCNA R&S, CCNA CyberOps, GMON, GPEN, GCFE, TPN, CEH, CEI, VCP-DCV, CHPA, PenTest+, Project+, and more.
APT Hunting with Splunk
John Stoner, Principal Security Strategist at Splunk
Interested in practicing your hunting skills? If so, this is the workshop for you. Using a real-worldish dataset, this workshop will teach you how to hunt the “fictional” APT group Violent Memmes. We discuss the Diamond model, building hypotheses, LM Kill Chain, and MITRE ATT&CK and how these concepts can frame your hunting. Using Splunk, we will hunt for APT activity riddling a small startup's environment. During the event, we will be presented with a "notable event" and pull on that string to conduct our own hunts based on indicators that we uncover or are identified. Depending on the hunt, we will uncover persistence, exfiltration, c2 and other adversary tactics. We may even find some PowerShell scripts. We will regroup and review the specific hunt conducted and discuss the timeline of events, a narrative that could be shared with others on your team, the artifacts that were uncovered to better identify potential future hunts, ATT&CK techniques referenced as well as what could be operationalized. At the end, we will highlight some additional datasets and content that you can take with you and try newly learned techniques yourself.
John Stoner (Twitter: @stonerpsu) is a Principal Security Strategist at Splunk where he enjoys writing, problem solving and building stuff, including APT Scenarios. When not doing cyber things, you can find him watching his boys play hockey, reading or binge-watching TV series that everyone else has already seen.
Security Investigations with Splunk
Robert Wagner, Splunk and Co-Founder of Hak4Kidz
Investigating with Splunk is a hands-on workshop designed to familiarize participants with how to investigate incidents using Splunk and open source. This workshop provides users a way to gain experience searching in Splunk to answer specific questions related to an investigation. These questions are similar to what would be asked in their own organizations. The workshop leverages the popular Boss of the SOC (BOTS) dataset in a question-and-answer format. Users will leave with a better understanding of how Splunk can be used to investigate in their enterprise. The class includes access to download the free “Investigating with Splunk” app that can be used to review the exercises after the class.
Robert Wagner (Twitter: @mr_minion) is a security professional with 15+ years of InfoSec experience. He is a co-founder of the “Hak4Kidz” charity, a co-organizer of BurbSec and BurbSecCon in Chicago, and is on the Board of Directors of the ISSA Chicago Chapter.
Intrusion Analysis and Threat Hunting with Suricata
Josh Stroschein, Director of IT Training at Open Information Security Foundation (OISF)
Peter Manev, CSO of Stamus Networks
In today’s threat landscape, sophisticated adversaries have routinely demonstrated the ability to compromise enterprise networks and remain hidden for extended periods of time. In Intrusion Analysis and Threat Hunting with open-source Tools, you will learn how to dig deep into network traffic to identify key evidence that a compromise has occurred, learn how to deal with new forms of attack, and develop the skills necessary to proactively search for evidence of new breaches. We will explore key phases of adversary tactics and techniques - from delivery mechanisms to post-infection traffic to get hands-on analysis experience. Open-source tools such as Suricata and Moloch will be utilized to generate data, perform exhaustive traffic analysis, and develop comprehensive threat hunting strategies. By the end of this workshop, you will have the knowledge and skills necessary to discover new threats in your network.
Josh Stroschein (Twitter: @jstrosch) is an experienced malware analyst and reverse engineer and has a passion for sharing his knowledge with others. He is the Director of Training for OISF, where he leads all training activity for the foundation and is also responsible for academic outreach and developing research initiatives. Josh is also an Associate Professor of Cyber Security at Dakota State University where he teaches malware analysis and reverse engineering, an author on Pluralsight, and a threat researcher for Bromium.
Peter Manev (Twitter: @pevma) is a co-founder of Stamus Networks, where he acts as CSO. He has been an active OISF member for a decade and has a 15 year-long record of activity in the field of IT security. An adamant admirer and explorer of innovative open-source security software, Peter is also the lead developer of SELKS.
Hands-On TCP Deep Dive with Wireshark
Chris Greer, Network Analyst and Wireshark Instructor at Packet Pioneer
A solid understanding of how TCP works is critical for anyone interested in cybersecurity. Almost all enumeration, incident response, and traffic forensics require the analyst to dig into and interpret TCP flows. In this video we will take a look at how TCP is used to investigate and establish connections, how data is transmitted and acknowledged, how connections are torn down, and what problem indicators should catch our eye in Wireshark. This video welcomes all cybersecurity and Wireshark experience levels.
Chris Greer is a network analyst and Wireshark instructor for Packet Pioneer, a Wireshark University partner. He has focused much of his career at the transport layer, specifically TCP, specializing in how this core protocol works to deliver applications, services, and attacks between systems. Chris is a regular speaker at Sharkfest - the Wireshark Developer and User Conference, as well as an author for Pluralsight.
First Batch of Accepted Packet Hacking Village Talks at DEF CON 29 Announced
Schedules of talks and events at the Packet Hacking Village are available at https://www.wallofsheep.com/pages/dc29. More talks will be added soon. All talks will be streamed on YouTube, Twitch, Facebook, and Periscope.
*nix Processes. Starting, Stopping, and Everything In Between
Nick Roy
Core Topic: Operating Systems: *nix
Recording discusses Linux and Unix processes, starting with a high level overview of what a process is and what the key components are. We then take a look at how the operating system manages multiple processes, what are the main components of a running process, and finally some common syscalls used in Linux when creating processes. Finally, we look at a few code samples to show how these calls are used with a simple shell. All code can be found here to compliment the video: https://github.com/superducktoes/syscall_processes
Nick Roy (Twitter: @superducktoes) currently works for a global security vendor creating training content and researching new attacker patterns and techniques. Previously he worked at an automation platform startup teaching people about the joys and benefits of automation. While not working he lives in Boston with his wife and two cats hunting out the best dive bars in Boston and solving math problems on college chalkboards overnight.
Internet Protocol (IP)
Roy Feng
Core Topic: Core Networking
The Internet Protocol is one of the foundational protocols of the Internet, and is what keeps devices connected. This video talks about the fundamentals of the Internet Protocol.
Roy Feng (Twitter: @LPF613) is a networking and cybersecurity enthusiast. He has six years of experience working as a network engineer and one year working in threat intelligence. His latest role is at a managed security service provider, where he leads a team of incident responders and threat hunters to help investigate and respond to incidents as well as hunt for threats in customer environments. In his spare time, Roy can be seen building and maintaining his home lab, and learning about and tinkering with the latest and greatest technologies.
Linux Binary Analysis w/ Strace
Jared Stroud, Lacework
Core Topic: File Analysis
The strace utility allows for deep insight into what an application is doing on a nix host. While the amount of data produced can be overwhelming, in this video I'll demonstrate how to filter, log and obtain relevant information for a wide variety of use cases around file analysis. From diagnosing a bisheaving application, to revealing a malware's secrets. This video will give a practical introduction in using strace to spy on *nix applications at the syscall level. All resources can be found here: https://www.github.com/lacework-dev/strace_lab_PUBLIC
Jared Stroud (Twitter: @DLL_Cool_J) is a Cloud Security Researcher at Lacework where he focuses on emerging Linux and Cloud platform threats. Previously, he worked at The MITRE Corporation where he contributed Unix and Windows tooling for the ATT&CK Fin7/CARBANAK Evaluation and the Open Source adversary emulation utility CALDERA.
MITRE Engage: A Framework for Adversary Engagement Operations
Stan Bar, Capability Area Lead, Cyber Denial, Deception, and Adversary Engagement, The MITRE Corporation
Gabby Raymond, Co-Capability Area Lead, Cyber Denial, Deception, and Adversary Engagement, The MITRE Corporation
Maretta Morovitz, Senior Cyber Security Engineer, The MITRE Corporation
Core Topic: File/Network Monitoring
For 10+ years MITRE has been engaged in denial, deception, and adversary engagement operations for internal defense and research purposes. We have created MITRE Engage as a framework for planning and communicating about adversary engagement operations. In our talk we include:
- A brief overview of what we mean when we say denial, deception, and adversary engagement
- Our vision for the future and why we think this technology matters
- A brief history of our past experiences (and failures) in this space and how that shaped where we are today
- The official release of MITRE Engage 0.9 Beta and ask for community feedback
- A fictional walkthrough of how you can use Engage to get started in adversary engagement operations
Dr. Stanley Barr is a three-time graduate of University of Massachusetts Lowell. He has a BS in Information Sciences, an MS in Mathematics, and a PhD in Computer Science. He has coauthored papers in malware analysis, barrier coverage problems, expert systems for network security, and robotic manufacturing. He has spoken at MILCOM and been a panelist for several conferences. Additionally, he has appeared on several podcasts on adversary engagement and presented at TEDx. Currently, he is a Principal Scientist at The MITRE Corporation. He currently is the Capability Area Leader for Cyber Denial, Deception, and Adversary Engagement. Stan lives with his wife, 5 rescue dogs, and 15 chickens.
Gabby Raymond is a two-time graduate from Tufts University. She holds a B.S. in Mathematics and Computer Science and a M.S. in Computer Science. Her research has spanned topics in intrusion detection, cyber-physical systems, and machine learning applications for security. Gabby recently co-authored a Choose Your Own Adventure style book called "The Toolbox of Innovation" with members of MITRE's Innovation Toolkit team. Outside of work, Gabby enjoys knitting and judging science fairs. Gabby is the Co-Capability Area Lead for Cyber Deception and Adversary Engagement at The MITRE Corporation.
Maretta Morovitz is a graduate of Tufts University School of Engineering, where she graduated with a degree in Computer Science. She is a Senior Cyber Security Engineer at the MITRE Corporation where she works in the areas of adversary engagement, malware analysis, and reverse engineering. She is a founding member of MITRE's Cyber Deterrence and Adversary Management (CDAM) team and has helped shape MITRE's adversary engagement work for the last two years. She was recently named as one fo the AFCEA 40 Under 40 Awardees for 2021. Outside of work you can find her nerding out about the latest Brandon Sanderson novel, still anxiously awaiting her letter from Hogwarts, or snuggling with her dog and hedgehog.
RCE via Meow Variant along with an Example 0day
Özkan Mustafa AKKUŞ, Senior Cyber Security Consultant and Vulnerability Researcher at Turk Telekom
Core Topic: Operating Systems: *nix
I will touch Some Alternative Bypass Restriction Techniques. Then I will present a vulnerability of Ericsson Network Location that provides the infrastructure of the research and we are going to touch on the meow variant with details through this vulnerability Towards the end we are going to prepare a Metasploit module and exploit the vulnerability.
Ozkan (Twitter: @ehakkus) is a vulnerability researcher and senior cyber security consultant in Turkey. Ozkan publishes security vulnerabilities on international platforms that he has discovered. He shares his experiences and works on his personal blog (https://www.pentest.com.tr). He gave training and presentations in many universities and institutions in his country. In addition to these studies, He gave the presentation of "The Vulnerability That Gmail Overlooked and Enabling Threat Hunting" in Packet Hacking Village at DEF CON 28 and "0day Hunting and RCE Exploitation in Web Applications" in AppSec Village at DEF CON 27.
Seeing the Forest Through the Trees – Foundations of Event Log Analysis
Jake Williams, CTO of BreachQuest
Core Topic: System Forensics
During an incident, everyone knows you need to review the logs – but what are they actually telling you? There's a wealth of information to be had in your logs event logs, but most analysts miss the forest because they don't understand the trees. In this talk, Jake will walk you through some of the most impactful event logs to focus on in your analysis. We'll target some old favorites covering login events, service creation, and process execution. We'll also examine task scheduler logs, useful in uncovering lateral movement and privilege escalation. Finally, we'll discuss some of the new event logs available in Windows 10 (if only you enable them first). If you don't want to be barking up the wrong tree during your next insider investigation or getting axed because you failed to identify the lateral movement attempts, make sure to watch this video.
Jake Williams (Twitter: @malwarejake) is an incident responder, red teamer, occasional vCISO, and prolific infosec shitposter. He has traveled the world, but isn't welcome in China or Russia (and avoids most countries they have extradition treaties with). When not speaking at a conference like this one, it's a good bet that Jake is engaged in hand to hand combat with an adversary rooted deep in a network or engineering ways to keep them out. Jake's career in infosec started in the intelligence community, but has taken around the world securing networks of all shapes and sizes, from utilities to hospitals to manufacturing plants.
Seeing Through The Windows: Centralizing Windows Logs For Greater Visibility
Matthew Gracie, Senior Engineer at Security Onion Solutions
Core Topic: Operating Systems: Windows
This talk is a brief summary of how to collect and centralize Windows Event Logs for analysis and free tools that can be used to do so. There is also a demonstration of how to use Elastic Stack to investigate an incident using these collected logs.
Matthew Gracie (Twitter: @InfosecGoon) has over a decade of experience in information security, working to defend networks in higher education, manufacturing, and financial services. He is currently a Senior Engineer at Security Onion Solutions and the founder of the Infosec 716 monthly meetup. Matt enjoys good beer, mountain bikes, Debian-based Linux distributions, and college hockey.
The War for Control of DNS Encryption
Dr. Paul Vixie, Chairman and CEO and Cofounder of Farsight Security, Inc.
Core Topic: Core Networking
Pervasive monitoring of the Internet by both government, corporate, and criminal actors has triggered an encryption wavefront as wide as the Internet itself. DNS, as the map of the Internet's territory, is seen as especially sensitive and there are now several competing encryption standards waiting to be deployed. In this short talk, Dr. Vixie will explain the original problem, describe the protocol-level solutions, and then show how vendors like Google, Mozilla Corporation, Microsoft, and Apple are deploying these technologies across their product lines. Opinions may also be offered.
Dr. Paul Vixie (Twitter: @PaulVixie) is an Internet pioneer. Currently, he is the Chairman, Chief Executive Officer and Cofounder of Farsight Security, Inc. He was inducted into the Internet Hall of Fame in 2014 for work related to DNS and DNSSEC. Dr. Vixie is a prolific author of open-source Internet software including BIND, and of many Internet standards documents concerning DNS and DNSSEC. In addition, he founded the first anti-spam company (MAPS, 1996), the first non-profit Internet infrastructure software company (ISC, 1994), and the first neutral and commercial Internet exchange (PAIX, 1991). He earned his Ph.D. from Keio University.
Time For Something New: Call For Presentations at the Packet Hacking Village
Security education is the mission of the Packet Hacking Village and the Wall of Sheep. We also take great pride in being a welcoming village for newcomers to DEF CON and to the Cyber Security field. We aim to act as a bridge between our visitors' existing knowledge and a better understanding of security topics by providing both knowledge of core fundamental concepts as well as advanced topics. Each year, there are thousands of newcomers into the Cyber Security field --technical or non-technical. We want to make sure that everyone has a solid foundation in Cyber Security. To that end, we're looking for pre-recorded talks in a 10-12 minute, 25-30 minute, OR 45-50 minute length, to teach our viewers something about one of these fundamental topics:
- Disk structures
- File systems
- Core networking concepts
- Operating Systems: *nix
- Operating Systems: Windows
- Operating Systems: macOS
- Code/cipher/hash fundamentals
- File analysis
- Web traffic fundamentals
- Network capture fundamentals
- Email fundamentals
- File/network/system forensics
- File/network monitoring
We have identified these topics as the fundamental pillars of knowledge in Cyber Security. Our Packet Detective, Packet Inspector, and Capture The Packet events each provide attendees a way to apply knowledge from these topics and more in an engaging learning environment. Our goal is to build a glossary of fundamentals for Cyber Security people of all kinds: students, practitioners, teachers, lawmakers, government officials, and professionals.
Product or vendor related pitches are not welcomed.
To submit a talk, please provide the following information and link to presentation video in the form below to cfp2021[at]wallofsheep[dot]com. The Call for Presentations will close on Friday, July 30th, at 11:59 PM PDT. The list of talks will be finalized and published on Sunday, August 1st.
SPEAKER NAME:
SPEAKER TITLE AND COMPANY (IF APPLICABLE):
SPEAKER EMAIL ADDRESS:
SPEAKER TWITTER NAME (IF YOU WANT IT KNOWN IF YOU ARE ACCEPTED):
NAME OF PRESENTATION:
WHICH ONE OF THE CORE TOPICS DOES YOUR VIDEO FIT INTO (CHECK ONE ONLY):
- Disk structures
- File systems
- Core networking concepts
- Operating Systems: *nix
- Operating Systems: Windows
- Operating Systems: macOS
- Code/cipher/hash fundamentals
- File analysis
- Web traffic fundamentals
- Network capture fundamentals
- Email fundamentals
- File/network/system forensics
- File/network monitoring
BRIEF DESCRIPTION OF YOUR VIDEO:
SPEAKER'S BIO:
This text will be used for the website and printed materials and should be written in the third person. Cover any professional history that is relevant to the presentation, including past jobs, tools that you have written, etc. Let people know who you are and why you are qualified to speak on your topic. Presentations that are submitted without biographies will not be considered.
WHERE TO DOWNLOAD YOUR VIDEO (e.g., Box, Dropbox, Google Drive, YouTube --unlisted), PROVIDE LINK:
As for video format, please use MP4.
TERMS AND CONDITIONS
By submitting you agree to the Terms and Conditions below. Please read and accept these terms by inserting your name in the appropriate area, otherwise your application will be considered incomplete and returned to you.
GRANT OF COPYRIGHT USE
I warrant that the above work has not been previously published elsewhere, or if it has, that I have obtained permission for its publication Aries Security, LLC. and that I will promptly supply Aries Security, LLC. with wording for crediting the original publication and copyright owner. If I am selected for presentation, I hereby give Aries Security, LLC. permission to duplicate, record and redistribute this presentation, which includes, but is not limited to, the conference proceedings, conference CD, video, audio, and hand-outs to the conference attendees for educational, on-line, and all other purposes.
Call for Hands-On Virtual Workshops at Packet Hacking Village at DEF CON 29
Overview
The Wall of Sheep would like to announce a call for workshops at DEF CON 29, "You Can't Stop the Signal." This hybrid conference will take place from Thursday, August 5 to Sunday, August 8, 2021. The Packet Hacking Village Virtual Workshops' goal is to deliver hands-on virtual training sessions that increase security awareness and provide skills to help bridge the gap between existing knowledge and more advanced topics with the intent to allow for immediate application after the conference. Our audience ranges from those new to security to the most seasoned security practitioners. Introductory workshops are welcome! A nominal fee will be charged for advanced registration of these workshops. However, all proceeds will go directly to The National Upcycled Computing Collective. Here is your chance to give back to the community in multiple ways! Each student will have access to a Kali Virtual Machine (VM) and other VMs that the instructor requires. Teaching assistants will be available to provide students with essential support if necessary.
Potential topics could include:
- Fundamental networking skills (i.e. ports and protocols, OSI model, hardware, segmentation)
- Core routing skills (IPv4, IPv6)
- Web communication, and related protocols (i.e. TCP/IP, SMB, ARP, HTTP)
- Tools for network sniffing, intrusion detection, monitoring, reverse engineering, forensics, penetration testing, data collection, or visualization
- Purple teaming
- Secure Software Development
- Training in hacking/security tools and their usage in the corporate world
- Programming for security practitioners
- Tool/task automation and optimization
- File system fundamentals for forensics (i.e. NTFS, EXT3/4, HFS+, FAT, FAT32 ExFat)
- Incident response process and procedures
The Wall of Sheep will not accept product or vendor-related pitches. If your content is a thinly veiled advertisement for a product or service your company is offering, please do not apply!
The Call for Presentations will close on Friday, June 25, 2021, at 11:59 PM PDT. The list of talks will be finalized and published on Wednesday, July 21, 2021.
Speaking Format
Each teaching slot is 1, 1.5, or 2 hours maximum, including time for Q&A. If we have time and it is in line with our goals mentioned above, then there is a good chance you will be selected.
TO SUBMIT A WORKSHOP, PLEASE PROVIDE THE FOLLOWING INFORMATION IN THE FORM BELOW TO CFW2021[AT]WALLOFSHEEP[DOT]COM
PRIMARY SPEAKER NAME:
PRIMARY SPEAKER TITLE AND COMPANY (IF APPLICABLE):
PRIMARY SPEAKER EMAIL ADDRESS:
PRIMARY SPEAKER PHONE NUMBER (TO CONTACT YOU IF NECESSARY DURING THE CONFERENCE):
PRIMARY SPEAKER TWITTER NAME (IF YOU WANT IT KNOWN IF YOU ARE ACCEPTED):
ADDITIONAL SPEAKERS' NAME(S), TITLES, AND SOCIAL INFORMATION:
ADDITIONAL EMAIL ADDRESSES:
IS THERE A SPECIFIC DAY OR TIME YOU MUST SPEAK BY?
NAME OF WORKSHOP:
LENGTH OF WORKSHOP:
(1, 1.5, or 2 hours)
ABSTRACT:
Your abstract will be used for the website and printed materials. Summarize what your workshop will cover. Attendees will read this to get an idea of what they should know before your presentation and what they will learn after. Use this to inform about how technical your talk is. This abstract is the primary way people will be drawn to your session. CFW reviewers like to see what tools will be used and what materials you suggest reading in advance to get the most out of your presentation.
SPEAKER'S BIO(S):
This text will be used for the website and printed materials and should be written in the third person. Cover any professional history that is relevant to the presentation, including past jobs, tools that you have written, etc. Let people know who you are and why you are qualified to speak on your topic. Presentations that are submitted without biographies will not be considered.
DETAILED OUTLINE:
You must provide a detailed outline containing the main points and navigation through your workshop. Show how you intend to begin, where you intend to lead the audience, and how you plan to get there. The outline may be provided in a separate attachment and may be as simple as a text file or as detailed as a "bare bones" presentation. The better your outline then, the better we can review your presentation against other submissions (and the higher chance you have of being accepted).
SUBMISSION NOTE: Presentations that are submitted without abstracts, outlines, or speaker bios (e.g., that have only PDFs, PPTs, or white papers attached or only point to a URL) will not be considered.
SUPPORTING FILE(S):
Additional supporting materials such as code, white papers, proof of concept, etc., should be sent along with this email to cfw2021[at]wallofsheep[dot]com. Note that additional files that may help in the selection process should be included. We are not asking for a complete presentation for this initial submission. That will only be required if you are selected for presenting.
NOTE:
Attendees will be allowed to pre-register for the workshop prior to DEF CON; there will be a small charge with the proceeds going to a charity of the Packet Hacking Village's choice.
Terms and Conditions
By submitting, you agree to the Terms and Conditions below. Please read and accept these terms by inserting your name in the appropriate area; otherwise, your application will be considered incomplete and returned to you.
GRANT OF COPYRIGHT USE
I warrant that the above work has not been previously published elsewhere, or if it has, that I have obtained permission for its publication by Aries Security, LLC. and that I will promptly supply Aries Security, LLC. with wording for crediting the original publication and copyright owner. If I am selected for presentation, I hereby give Aries Security, LLC. Permission to duplicate, record, and redistribute this presentation, which includes, but is not limited to, the conference proceedings, conference CD, video, audio, and hand-outs to the conference attendees for educational, online, and all other purposes.
TERMS OF SPEAKING REQUIREMENTS
1. I will submit a completed (and possibly updated) presentation and a reference to all the tool(s), law(s), Web sites and/or publications referenced at the end of my talk and as described in this CFW submission by noon PDT, July 21, 2021.
2. I will submit a final Abstract and Biography to the Wall of Sheep by noon PDT, July 21, 2021.
3. I will include a detailed bibliography as either a separate document or contained within the presentation of all resources cited and/or used in my presentation.
4. I will complete my presentation within the time allocated to me - not running over the time allocation.
YES, I (INSERT PRIMARY SPEAKER NAME) HAVE READ AND AGREE TO THE GRANT OF COPYRIGHT USE.
I, (INSERT YOUR NAME HERE), HAVE READ AND UNDERSTAND AND AGREE TO THE TERMS AS DETAILED IN THE AGREEMENT TO TERMS OF SPEAKING REQUIREMENTS.
IN THE CASE THAT A SPEAKER IS A CHILD UNDER THE AGE OF 13 YEARS OLD: IN COMPLIANCE WITH THE CHILDREN'S ONLINE PRIVACY PROTECTION ACT (COPPA) REGULATIONS, https://www.ftc.gov/enforcement/rules/rulemaking-regulatory-reform-proceedings/childrens-online-privacy-protection-rule, ANY CHILD UNDER AGE 13 MUST HAVE PARENTAL CONSENT FOR THE COLLECTION, USE, OR DISCLOSURE OF THAT CHILD'S PERSONAL INFORMATION BY A WEBSITE. PARENT/GUARDIAN CONSENT: I (INSERT PARENT/GUARDIAN'S NAME HERE) AM THE PARENT OR GUARDIAN OF THE MINOR/S NAMED ABOVE. I HAVE READ AND UNDERSTAND AND AGREE TO THE TERMS AS DETAILED IN THE AGREEMENT TO TERMS OF SPEAKING REQUIREMENTS.
Packet Hacking Village at DEF CON 29
We hope this finds you and your loved ones well. We thank you for your continuing support after all these years. We miss you all, and look forward to seeing each other in-person soon. The format of DEF CON 29 hasn’t been officially announced yet, but regardless of format (in-person, virtual, combination of the two), Packet Hacking Village will be ON for DEF CON 29. At the very least, we will be having the following events:
- Capture The Packet (CTP)
- Packet Detective (PD)
- Packet Inspector (PI)
More events, including new ones, will be announced soon. We look forward to seeing you all in some capacity.
Packet Inspector
The perfect introduction to network analysis, sniffing, and forensics. Do you want to understand the techniques people use to tap into a network, steal passwords and listen to conversations? Packet Inspector is the place to develop these skills! For well over a decade, the Wall of Sheep has shown people how important it is to use end-to-end encryption to keep sensitive information like passwords private. Using a license of the world famous Capture The Packet engine from Aries Security, we have created a unique way to teach hands-on skills in a controlled real-time environment.
Packet Detective
Looking to upgrade your skills or see how you would fare in Capture The Packet? Come check out what Packet Detective has to offer! A step up in difficulty from Packet Investigator, Packet Detective will put your network hunting abilities to the test with real-world scenarios at the intermediate level. Take the next step in your journey towards network mastery in a friendly environment still focused on learning and take another step closer to preparing yourself for the competitive environment of Capture The Packet.
Capture The Packet
Come compete in the world's most challenging cyber defense competition based on the Aries Security Cyber Range. Tear through the challenges, traverse a hostile enterprise class network, and diligently analyze what is found in order to make it out unscathed. Not only glory, but prizes await those that emerge victorious from this upgraded labyrinth, so only the best prepared and battle hardened will escape the crucible.
UPDATED Call for Hands-On Workshops at Packet Hacking (Virtual) Village Talks at DEF CON 28
Overview
The Wall of Sheep would like to announce a call for Workshops at DEF CON 28 “Safe Mode.” This virtual conference will take place from Thursday, August 6th to Sunday, August 9th. The Packet Hacking Village Workshops’ goal is to deliver hands-on training sessions that increase security awareness and provide skills that can be immediately applied after the conference. Our audience ranges from those who are new to security to the most seasoned practitioners in the security industry. Introductory workshops are welcome! A very nominal fee will be charged for advanced registration of these workshops. However, all proceeds will go directly to The National Upcycled Computing Initiative (NUCC). This is your chance to give back to the community in multiple ways!
Each student will have access to a Kali virtual machine (VM) and other VMs that are required by the instructor. Teaching assistants will be available to provide basic support if necessary.
Topics of interest include:
- Tools for Network sniffing, intrusion detection, monitoring, reverse engineering, forensics, penetration testing, data collection and visualization
- Purple teaming
- Secure Software Development
- Training in hacking/security tools and their usage in the corporate world
- Programming for security practitioners
- Tool/task automation and optimization
- Incident response process and procedures
The Wall of Sheep will not accept product or vendor related pitches. If your content is a thinly-veiled advertisement for a product or service your company is offering, please do not apply!
The Call for Presentations will close on Friday, June 26th at 11:59 PM PDT. The list of talks will be finalized and published on Wednesday, July 15th.
Speaking Format
Each teaching slot is 1, 1.5 or 2 hours maximum, including time for Q&A. If we have time and it is in line with our goals mentioned above, then there is a good chance you will be selected.
To submit a workshop, please provide the following information in the form below to cfw2020[at]wallofsheep[dot]com
Primary Speaker Name:
Primary Speaker Title and Company (if applicable):
Primary Speaker Email Address:
Primary Speaker Phone Number (to contact you if necessary during the conference):
Primary Speaker Twitter name (if you want it known if you are accepted):
Additional Speakers' name(s), titles, and social information:
Additional Email Addresses:
Is there a specific day or time you MUST speak by?
Name of Workshop:
Length of Workshop:
(1, 1.5, or 2 hours)
Abstract:
Your abstract will be used for the website and printed materials. Summarize what your workshop will cover. Attendees will read this to get an idea of what they should know before your presentation, and what they will learn after. Use this to inform about how technical your talk is. This abstract is the primary way people will be drawn to your session. CFW reviewers like to see what tools will be used and what materials you suggest to read in advance to get the most out of your presentation.
Speaker's Bio(s):
This text will be used for the website and printed materials and should be written in the third person. Cover any professional history that is relevant to the presentation, including past jobs, tools that you have written, etc. Let people know who you are and why you are qualified to speak on your topic. Presentations that are submitted without biographies will not be considered.
Detailed Outline:
You must provide a detailed outline containing the main points and navigation through your workshop. Show how you intend to begin, where you intend to lead the audience and how you plan to get there. The outline may be provided in a separate attachment and may be as simple as a text file or as detailed as a "bare bones" presentation. The better your outline then the better we are able to best review your presentation against other submissions (and the higher chance you have of being accepted). SUBMISSION NOTE: Presentations that are submitted without abstracts, outlines, or speaker bios (e.g., that have only PDFs, PPTs, or white papers attached or only point to a URL) will not be considered.
Supporting File(s):
Additional supporting materials such as code, white papers, proof of concept, etc. should be sent along with this email to cfw2020[at]wallofsheep[dot]com. Note that additional files that may help in the selection process should be included. We are not asking for a complete presentation for this initial submission. That will only be required if you are selected for presenting.
Note:
Attendees will be allowed to pre-register for the workshop prior to DEF CON; there will be a small charge with the proceeds going to a charity of the Packet Hacking Village's choice.
Terms and Conditions
By submitting you agree to the Terms and Conditions below. Please read and accept these terms by inserting your name in the appropriate area, otherwise your application will be considered incomplete and returned to you.
Grant of Copyright Use
I warrant that the above work has not been previously published elsewhere, or if it has, that I have obtained permission for its publication Aries Security, LLC. and that I will promptly supply Aries Security, LLC. with wording for crediting the original publication and copyright owner. If I am selected for presentation, I hereby give Aries Security, LLC. permission to duplicate, record and redistribute this presentation, which includes, but is not limited to, the conference proceedings, conference CD, video, audio, and hand-outs to the conference attendees for educational, on-line, and all other purposes.
Terms of Speaking Requirements
1. I will submit a completed (and possibly updated) presentation and a reference to all of the tool(s), law(s), Web sites and/or publications referenced to at the end of my talk and as described in this CFW submission by noon PST, July 15, 2020.
2. I will submit a final Abstract and Biography to the Wall of Sheep by noon PST, July 15, 2020.
3. I will include a detailed bibliography as either a separate document or included within the presentation of all resources cited and/or used in my presentation.
4. I will complete my presentation within the time allocated to me - not running over the time allocation.