Packet Hacking Virtual Village at DEF CON 28 Safe Mode
The Packet Hacking Village at DEF CON 28 #SafeMode will be on Discord. The Packet Hacking Village Discord Channel is available at https://discord.com/channels/708208267699945503/708242376883306526. Our village hours are:
- Friday, August 7th: 9am-7pm PDT
- Saturday, August 8th: 9am-7pm PDT
- Sunday, August 9th: 9am-3pm PDT
All times are in PDT. Schedules are subject to change.
Events and Contests
- Packet Inspector (#phv-packet-inspector-text on Discord)
- Packet Detective (#phv-packet-detective-text on Discord; Human+)
- Capture The Packet (#cpt-text on Discord; Human+)
- Wall of Sheep DJ Community - WoSDJCo (#-wosdjco-text on Discord)
- Hands-On Workshops Schedule and Registration (#phv-workshops-text on Discord)
- Talks Schedule (#phv-talks-text on Discord; Human+)
- Walkthrough Workshops (#cpt-text on Discord; Human+)
Packet Inspector
The perfect introduction to network analysis, sniffing, and forensics. Do you want to understand the techniques people use to tap into a network, steal passwords and listen to conversations? Packet Inspector is the place to develop these skills! For well over a decade, the Wall of Sheep has shown people how important it is to use end-to-end encryption to keep sensitive information like passwords private. Using a license of the world famous Capture The Packet engine from Aries Security, we have created a unique way to teach hands-on skills in a controlled real-time environment.
Packet Detective
Looking to upgrade your skills or see how you would fare in Capture The Packet? Come check out what Packet Detective has to offer! A step up in difficulty from Packet Investigator, Packet Detective will put your network hunting abilities to the test with real-world scenarios at the intermediate level. Take the next step in your journey towards network mastery in a friendly environment still focused on learning and take another step closer to preparing yourself for the competitive environment of Capture The Packet.
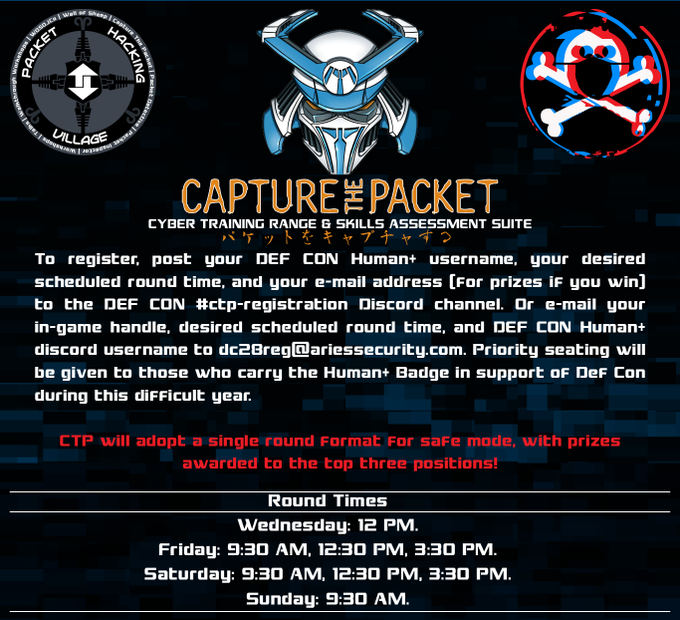
Capture The Packet
Come compete in the world's most challenging cyber defense competition based on the Aries Security Cyber Range. Tear through the challenges, traverse a hostile enterprise class network, and diligently analyze what is found in order to make it out unscathed. Not only glory, but prizes await those that emerge victorious from this upgraded labyrinth, so only the best prepared and battle hardened will escape the crucible.
Wall of Sheep DJ Community - WoSDJCo
Come chill with us while we play all your favorite Deep, underground house, techno, breaks, and DnB beats mixed live all weekend by your fellow hacker DJs. We will provide the soundtrack for all your epic PHV hax, just like we do every year.
Walkthrough Workshops
The Packet Hacking Village brings you the Walkthrough Workshops, where you will go on a self-guided journey to building your own honey pot, taking it live and hopefully trapping some unsuspecting users. Fear not though, like with all our other training events, we will have helpful and knowledgeable staff on hand to assist you along the way!
Workshops Schedule
Registration on Eventbrite: https://www.eventbrite.com/e/packet-hacking-virtual-village-workshops-at-dc-28-safe-mode-ticket-sales-registration-114100325144
| Friday, August 7th | |
|---|---|
| 13:00 - 15:00 |
Intrusion Analysis and Threat Hunting with Open Source Tools Josh Stroschein, Peter Manev |
| 16:00 - 18:00 |
Violent Python 3 Sam Bowne, Elizabeth Biddlecome, Kaitlyn Handleman, Irvin Lemus |
| Saturday, August 8th | |
| 09:00 - 11:00 |
Writing Wireshark Plugins for Security Analysis Nishant Sharma, Jeswin Mathai |
| 13:00 - 15:00 |
Wireshark for Incident Response & Threat Hunting Michael Wylie |
| 16:00 - 18:00 |
Advanced APT Hunting with Splunk Matt Toth, Robert Wagner |
| Sunday, August 9th | |
| 09:00 - 13:00 |
Bad Active Directory (BAD) Dhruv Verma, Michael Roberts, Kuan Xiang Wen |
Workshops Abstracts and Bios
Intrusion Analysis and Threat Hunting with Open Source Tools
Josh Stroschein, Director of Training, Open Information Security Foundation (OISF) / Suricata
Assisted by Peter Manev
In today's threat landscape, sophisticated adversaries have routinely demonstrated the ability to compromise enterprise networks and remain hidden for extended periods of time. In Intrusion Analysis and Threat Hunting with Open Source Tools, you will learn how to dig deep into network traffic to identify key evidence that a compromise has occurred, learn how to deal with new forms of attack, and develop the skills necessary to proactively search for evidence of new breaches. We will explore key phases of adversary tactics and techniques - from delivery mechanisms to post-infection traffic to get hands-on analysis experience. Open-source tools such as Suricata and Moloch will be utilized to generate data, perform exhaustive traffic analysis, and develop comprehensive threat hunting strategies. By the end of this workshop, you will have the knowledge and skills necessary to discover new threats in your network.
Josh Stroschein is an experienced malware analyst and reverse engineer who has a passion for sharing his knowledge with others. He is the Director of Training for OISF, where he leads all training activities for the foundation and is also responsible for academic outreach and developing research initiatives. Josh is an accomplished trainer, providing training in the aforementioned subject areas at BlackHat, DerbyCon, Toorcon, Hack-In-The-Box, Suricon and other public and private venues. Josh is an Assistant Professor of Cyber Security at Dakota State University where he teaches malware analysis and reverse engineering, an author on Pluralsight, and a threat researcher for Bromium.
Peter Manev has been involved with Suricata IDS/IPS/NSM from its very early days in 2009 as QA lead, currently a Suricata executive council member. Peter has 15 years experience in the IT industry, including enterprise and government level IT security practice. As an adamant admirer and explorer of innovative open source security software he is also one of the creators of SELKS - an open source threat detection security distro. He is also one of the founders of Stamus Networks, a company providing security solutions based on Suricata.
Violent Python
Sam Bowne, Instructor, City College San Francisco
Assisted by Elizabeth Biddlecome, Part-time Instructor, City College San Francisco; Elizabeth Biddlecome, and Irvin Lemus
Even if you have never programmed before, you can quickly and easily learn how to make custom hacking tools in Python. We build tools that perform port scanning, brute-force attacks, crack password hashes, and XOR encryption. Python is among the top three programming languages in the world, for good reason: it's the easiest language to use for general purposes.
Sam Bowne (Twitter: @sambowne has been teaching computer networking and security classes at City College San Francisco since 2000, and is the founder of Infosec Decoded, Inc. He has given talks and hands-on trainings at Black Hat USA, RSA, DEF CON, DEF CON China, HOPE, and many other conferences. Credentials: PhD, CISSP, DEF CON Black Badge Co-Winner
Elizabeth Biddlecome is a consultant and instructor, delivering technical training and mentorship to students and professionals. She is a senior instructor for Infosec Decoded, Inc. She leverages her enthusiasm for architecture, security, and code to design and implement comprehensive information security solutions for business needs. Elizabeth enjoys wielding everything from soldering irons to scripting languages in cybersecurity competitions, hackathons, and CTFs.
Irvin Lemus has served clients throughout California, providing valuable professional services that bring peace of mind to clients as well as security against the constant threats with our ever-connected world.
Kaitlyn Handleman is a Professional Red Teamer.
Writing Wireshark Plugins for Security Analysis
Nishant Sharma, R&D Manager, Pentester Academy
Jeswin Mathai, Security Researcher, Pentester Academy
Network traffic always proves to be a gold mine when mined with proper tools. There are various open source and paid tools to analyze the traffic but most of them either have predefined functionality or scalability issues or one of a dozen other problems. And, in some cases when we are dealing with non-standard protocols, the analysis becomes more difficult. But, what if we can extend our favorite traffic analysis tool Wireshark to accommodate our requirements? As most people know, Wireshark supports custom plugins created in C and Lua which can be used to analyze or dissect the packets. In this workshop, we will learn the basics of Wireshark plugins and move on to create different types of plugins to perform dissection of non-standard protocol, provide macro statistics, detect attacks etc. We will use examples of older and newer protocols (including non-standard ones) to understand the plugin workflow and development.
Nishant Sharma (Twitter: @wifisecguy) is an R&D Manager at Pentester Academy and Attack Defense. He is also the Architect at Hacker Arsenal where he leads the development of multiple gadgets for WiFi pentesting such as WiMonitor, WiNX and WiMini. He also handles technical content creation and moderation for Pentester Academy TV. He has 7+ years of experience in information security field including 5+ years in WiFi security research and development. He has presented/published his work at Blackhat USA/Asia, DEF CON China, Wireless Village, IoT village and Demo labs (DEFCON USA). Prior to joining Pentester Academy, he worked as a firmware developer at Mojo Networks where he contributed in developing new features for the enterprise-grade WiFi APs and maintaining the state of art WiFi Intrusion Prevention System (WIPS). He has a Master's degree in Information Security from IIIT Delhi. He has also published peer-reviewed academic research on HMAC security. His areas of interest include WiFi and IoT security, AD security, Forensics and Cryptography.
Jeswin Mathai (Twitter: @jeswinmathai) is a Researcher at Pentester Academy and Attack Defense. He has presented/published his work at DEF CON China, Blackhat Arsenal and Demo labs (DEFCON). He has a Bachelor's degree from IIIT Bhubaneswar. He was the team lead at InfoSec Society IIIT Bhubaneswar in association with CDAC and ISEA, which performed security auditing of government portals, conducted awareness workshops for government institutions. He was also the part of team Pied Piper who won Smart India Hackathon 2017, a national level competition organized by GoI. His area of interest includes Malware Analysis and Reverse Engineering, Cryptography, WiFi security and Web Application Security.
Wireshark for Incident Response & Threat Hunting
Michael Wylie, Director of Cybersecurity Services, Richey May Technology Solution
This workshop will take student's Wireshark skills to the next level with a heavy emphasis on incident response, threat hunting, and malicious network traffic analysis. We will begin with a brief introduction to Wireshark and other Network Security Monitoring (NSM) tools/concepts. Placement, techniques, and collection of network traffic will be discussed in detail. Throughout the workshop, we'll examine what different attacks and malware look like in Wireshark. Students will then have hands-on time in the lab to search for Indicators of Compromise (IOCs) and a potential breach to the network. There will be plenty of take-home labs for additional practice.
Michael Wylie (Twitter: @TheMikeWylie), MBA, CISSP is the Director of Cybersecurity Services at Richey May Technology Solutions. In his role, Michael is responsible for delivering information assurance by means of vulnerability assessments, cloud security, penetration tests, risk management, and training. Michael has developed and taught numerous courses for the U.S. Department of Defense, DEFCON, Universities, and for clients around the world. Michael is the winner of numerous SANS challenge coins and holds the following credentials: CISSP, CCNA R&S, CCNA CyberOps, GMON, GPEN, TPN, CEH, CEI, VCP-DCV, CHPA, PenTest+, Security+, Project+, and more.
Advanced APT Hunting with Splunk
Matt Toth, Security Strategist, Splunk
Assisted by Robert Wagner, Security Strategist
You wanna learn how to hunt the APTs? This is the workshop for you. Using a real-worldish dataset, this workshop will teach you how to hunt the "fictional" APT group Taedonggang. We discuss the Diamond model, hypothesis building, LM Kill Chain, and Mitre ATT&CK framework and how these concepts can frame your hunting. Using Splunk and OSINT, we will hunt for APT activity riddling a small startup's network. During the event, you will be presented a hypothesis and conduct your own hunts, whether it is for persistence, exfiltration, c2 or other adversary tactics. Heck, there might be some PowerShell to be found, too. We will regroup and review the specific hunt and discuss findings and what opportunities we have to operationalize these findings as well. At the end, we give you a dataset and tools to take home and try newly learned techniques yourself.
Matt Toth is a Security Strategist at Splunk with over 20 years of experience in the Information Technology industry, with a focus on Cyber Security. Working with the US Department of Defense, he has led teams in CyberWar simulations, and has advised senior leadership on new attack vectors and threat actors.
Robert Wagner is a security professional with 20+ years of InfoSec experience. He is a co-founder of "Hak4Kidz.com", an organizer with Burbsec and BurbSecCon in Chicago, and is on the Board of Directors of the ISSA Chicago Chapter.
Bad Active Directory (BAD)
Dhruv Verma, Senior Security Consultant, NCC Group
Assisted by Michael Roberts, Principal Security Consultant, NCC Group, and Kuan Xiang Wen, Security Consultant, NCC Group
This is an introductory to intermediate level Windows active directory (AD) training. The training has two parts: a lecture component, where we'll cover how active directory works and the core things you need to know to attack it effectively, and a series of hands-on labs modeled after real attacks we've performed on client environments. The training will be heavily lab focused, with each student receiving their own AWS environment to play with. The labs are based off of how real modern networks look, not example test environments, and successfully completing each lab involves chaining together multiple vulnerabilities in a realistic kill chain methodology to get domain admin.
Dhruv Verma is a Senior Security Consultant at NCC Group, an information security firm specializing in application, network, and mobile security. Dhruv has extensive experience performing infrastructure assessments with a special interest in Windows Active Directory environments and projects involving social engineering vectors. He has gotten domain admin on multiple client networks by chaining together vulnerabilities in a very unique and interesting fashion. For instance, Dhruv combined a misconfigured Jenkins server with a AWS IAM privilege escalation attack to gain Domain Admin on an enterprise network via a clone'n'pwn attack.
Michael Roberts is a Principal Security Consultant with NCC Group. Michael performs web, mobile application and network penetration tests, and has a passion for virtual reality and cooking outside of work life. Michael holds a bachelor's degree in computer and information technology from Purdue University.
Kuan Xiang Wen is a Security Consultant at NCC Group. Kuan has conducted some infrastructure assessments and first started BAD under the supervision of Dhruv and Michael as his intern project at NCC. Kuan is as exciting as Kashi cereal and likes to eat free food at hacker events.
Talks Schedule
Talks will be streamed on YouTube, Twitch, Facebook, and Periscope.
| Friday, August 7th | |
|---|---|
| 10:00 - 11:00 |
Media Analysis of Disinformation Campaigns Mike Raggo and Chet Hosmer |
| 13:00 - 14:00 |
Dumpster Fires: 6 Things About IR I Learned by Being a Firefighter Dr. Catherine Ullman |
| 16:00 - 17:00 |
Packet Acquisition: Building the Haystack Chris Abella and Pete Anderson |
| Saturday, August 8th | |
| 10:00 - 11:00 |
The Vulnerability That Gmail Overlooked and Enabling Threat Hunting Ozkan Mustafa Akkus |
| 13:00 - 14:00 |
The Worst Mobile Apps Sam Bowne |
| Sunday, August 9th | |
| 11:00 - 12:00 |
Take Down the Internet! With Scapy C8 (John Hammond) |
Talks Abstracts and Bios
Media Analysis of Disinformation Campaigns
Mike Raggo, Co-Founder, SilentSignals.com
Chet Hosmer, Owner, Python Forensics
In this session we'll focus on the media aspects of disinformation campaigns with deep analysis of altered images, audio, and video to uncover methods used to twist narratives and mislead perceptions surrounding topical news stories. We'll dive into the taxonomy of fake photos, deepfakes, phishing audio fraud attacks, keyword squatting malware, fake rallies, narrative laundering, nation state fake intelligence. and media generated to inspire mass hysteria. We'll then further categorize these threats by their TTPs and provide methods for enhancing detection and response strategies. Real world examples will be demonstrated to provide deep and tangible insights into this systemic problem.
Mike Raggo (Twitter: @MikeRaggo) has over 20 years of security research experience. Over the years he has uncovered numerous vulnerabilities in commercial networking, mobile, and security products. His current research focuses on multimedia disinformation campaigns. His research has been highlighted on television's CNN Tech, and numerous media publications including TIME, Forbes, Bloomberg, Dark Reading, TechCrunch, TechTarget, The Register, and countless others. Michael is the author of "Mobile Data Loss: Threats & Countermeasures" and "Data Hiding: Exposing Concealed Data in Multimedia, Operating Systems, Mobile Devices and Network Protocols" for Syngress Books, and is a contributing author for "Information Security the Complete Reference 2nd Edition". His Data Hiding book is also included at the NSA's National Cryptologic Museum at Ft. Meade. A former security trainer, Michael has briefed international defense agencies including the FBI, Pentagon, and Queensland Police; and is a former participating member of FSISAC/BITS and the PCI Council. He is also a frequent presenter at security conferences, including Black Hat, DEF CON, Gartner, RSA, DoD Cyber Crime, OWASP, HackCon Norway, and SANS. He was also awarded the Pentagon's Certificate of Appreciation.
Chet Hosmer (Twitter: @chethosmer) is an international author, educator & researcher, and founder of Python Forensics, Inc., a non-profit research institute focused on the collaborative development of open source investigative technologies using the Python programming language. Chet is also a Visiting Professor at Utica College in the Cybersecurity Graduate Program, where his research and teaching is focused on data hiding, active cyber defense and security of industrial control systems. Additionally, Chet is an Adjunct Professor at Champlain College in the Digital Forensics Graduate Program, where his research and teaching is focused on solving hard digital investigation problems using the Python programming language.
Dumpster Fires: 6 Things About IR I Learned by Being a Firefighter
Dr. Catherine J. Ullman, Sr. Information Security Forensic Analyst
Threats surround us like a ring of burning fire. Unfortunately, incident response doesn't come naturally to an operational mindset where the focus tends to be on reactive problem solving. As a volunteer firefighter for over twenty years, investigatorchic has learned a lot about what is and isnt effective. There are surprising parallels between fighting real-life fires and the fire-fighting that passes for today's incident response. For example, striking a balance between swift response and patient reflection is often the difference between life and death, in a very literal sense for the firefighter and a figurative sense for the security professional. It's also all too easy to get tunnel vision and focus on the wrong areas, costing precious time. The security world is full of dumpster fires these days, so join this session to learn from a good firefighter what makes a good security person.
Dr. Catherine J. Ullman (Twitter: @investigatorchi) is a security researcher, speaker, and Senior Information Security Forensic Analyst at University at Buffalo with over 20 years of highly technical experience. In her current role, Cathy is a data forensics and incident response (DFIR) specialist, performing incident management, intrusion detection, investigative services, and personnel case resolution in a dynamic academic environment. She additionally builds security awareness amongst faculty and staff via a comprehensive department-wide program which educates and informs users about how to prevent and detect social engineering threats, and how to compute and digitally communicate safely. Cathy has presented at numerous prestigious information security conferences including DEF CON and Hacker Halted. In her (minimal) spare time, she enjoys visiting her adopted two-toed sloth Flash at the Buffalo zoo, researching death and the dead, and learning more about hacking things to make the world a more secure place.
Take Down the Internet! With Scapy
John Hammond
You know Python remains a hacker's favorite language... and for both network defenders and attackers alike, Scapy shines as their favorite Python module! This talk introduces Scapy and its syntax, discusses and showcases multiple attacks that can be performed with Scapy (SYN flood, Ping of Death, DNS amplification attacks and more) as well as offering some defensive techniques to mitigate these attacks. These network attacks are often a "denial of service" and have dire consequences – so you choose your role as an attacker or defender, and be part of either the cause or the solution to take down the Internet!
John Hammond (Twitter: @_johnhammond) is a cybersecurity instructor, developer, red teamer, and CTF enthusiast. Cyber Training Academy curriculum developer and teacher for the Cyber Threat Emulation course, educating both civilian and military members on offensive Python, PowerShell, other scripting languages and the adversarial mindset. He personally developed training material and infosec challenges for events such as PicoCTF and the "Capture the Packet" competition at DEFCON US. John speaks at security conferences such as BsidesNoVA, to students at colleges such as the University of North Carolina Greensboro, and other events like the SANS Holiday Hack Challenge/KringleCon. He is an online YouTube personality to showcase programming tutorials, cyber security guides, and CTF video walkthroughs. John currently holds the following certifications: Security+, eJPT, CEH, PCAP, OSWP, OSCP, OSCE, and OSWE.
The Vulnerability That Gmail Overlooked and Enabling Threat Hunting
Özkan Mustafa Akkus, Vulnerability Researcher and Penetration Testing Expert, Barikat Cyber Security
The use and working logic of the SMTP protocol is very simple, but it poses different threats. Large e-mail infrastructures such as Gmail can forget important and critical points that may threaten the security of people while using this protocol. By explaining this primitive structure of the SMTP protocol, we will examine the vulnerability that I discovered in Gmail. We will also do live examples.
Ozkan (Twitter: @ehakkus) is a vulnerability researcher and penetration testing expert in Turkey. While studying sports sciences and technologies, he decided to leave the University and step into the world of Cyber Security. His purpose is to provide added value to the world of cyber security through the training he has given and the research he has conducted. Ozkan publish security vulnerabilities on international platforms that he has discovered. He shares his experiences and works on his personal blog https://www.pentest.com.tr. Ozkan also has many internationally recognized certificates such as OSWE, OSCE, OSCP, OSWP, CEH, CCNA, TSE-STU. He gave trainings and presentations in many universities and institutions in his country. In addition to these studies, He gave the presentation of "0day Hunting and RCE Exploitation in Web Applications" in AppSec Village at Defcon 27.
The Worst Mobile Apps
Sam Bowne, Founder, Infosec Decoded Inc.
I've audited hundreds of Android apps and now, thanks to the Checkra1n jailbreak, iOS apps as well. Many of these apps have security flaws such as exposing passwords on the phone or in network traffic, but a few of them are spectacularly insecure, exposing the entire user database to every user. I will explain how to perform simple tests to detect such errors and demonstrate them with live apps on both Android and iOS devices. Don't let this happen to your app!
Sam Bowne (Twitter: @sambowne has been teaching computer networking and security classes at City College San Francisco since 2000, and is the founder of Infosec Decoded, Inc. He has given talks and hands-on trainings at Black Hat USA, RSA, DEF CON, DEF CON China, HOPE, and many other conferences. Credentials: PhD, CISSP, DEF CON Black Badge Co-Winner
Packet Acquisition: Building the Haystack
Chris Abella, P SE, ExtraHop Networks
Pete Anderson, Sr. SE, ExtraHop Networks
Packet hacking doesn't happen without packets. There are multiple methods to get packets from a network; from local tcpdump and Wireshark all the way to enterprise wide tapping and span aggregation. In this talk, we'll discuss enterprise packet acquisition strategies and challenges, and the methods, tools, and techniques necessary to build the data foundation for effective network-based detection and forensics.
Garbage data in means garbage analysis out. Chris and Pete have spent decades working with Fortune 500 NOC and SOC teams to implement advanced packet analysis solutions, build better packet pipelines, and get more from those packets.